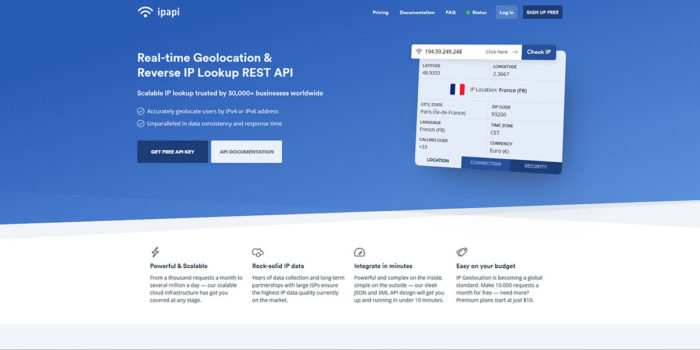
The REST API ipapi.com is one of the favorite tools in my API toolkit. It creates valuable sets of information from raw IP data. Geolocation lookup and IP address validation is automated by the service and it offers in excess of 45 data references per IP address that is processed, including connection, location, security, time zone and currency.
I recommend this tool for many reasons. Not only is it developed by apilayer, a well-known company, but it is also trusted by more than 30,000 projects around the world. The API is secure, scalable, accurate and resilient. The main reason I love ipapi.com, however, is that they assisted me in understanding my users and allows me to earn their trust.
Custom experiences and privacy, do they get along?
The internet could not exist without the IP protocol. The concept behind this protocol has largely remained the same ever since the first data packet was sent from a host to its destination. As privacy was not a concern at the time, it was strictly designed for utilitarian purposes.
By the time privacy implications of sharing a host’s IP address openly on the web were fully realized, this issue could no longer be addressed at the fundamental level. I have recently noticed that companies are becoming increasingly aware of data privacy and the potential implications of using data that was acquired without consent in services and products.
There is however also a lot of overemphasis in the marketplace. It is true that as IP data is a subset of private data, it is therefore a constituent element of data privacy. It is also true that service providers have a duty to take all reasonable steps to ensure the protection of private data exchanges. They should also use the transaction’s byproducts to provide the service their users expect.
In summary:
- IP data may be used to deliver a user experience
- IP data may not be used to trace users
- IP data may be used to target users, providing that their consent has been obtained
An example might clarify the issue. When mail is sent via the postal service, and a reply is expected, the sender shares their name and address with the recipient. When this happens, the sender trusts the recipient with private data. The mailman is also a trusted party in this equation. The same happens when users connect to an online service. They entrust the service with their IP address. The interactions between parties are in both cases based on benevolence, consent, reasonable expectations and reasonable interest.
This means that IP data can be used to:
- Redirect users to regional websites
- Calculate delivery prices and taxes in region specific currencies
- Make promotional offers to users from specific regions
- Deny service access to an IP or range of IPs
- Block IPs from specific regions
- Use weather widgets to display forecasts for specific regions
These uses are all anonymous and reasonable.
Can users be tracked and their privacy respected at the same time?
A booking site, for example, uses an algorithm with IP data in combination with weather data to suggest vacation rentals. The site is able to trace a user’s location to Norway and suggest that users with that IP, book a vacation in the Maldives. Would this use fit the benevolence, consent, reasonable expectations and reasonable interest scenario? Although it is a great idea to offer vacations at locations with a much better climate, this would be classified as non-consensual profiling and may result in angry and upset customers.
In another example, a supplier of kettles uses an algorithm that notices a returning user from a specific IP address. As there is no order on the system from that IP address, the algorithm is set to offer discount prices after the user has visited a certain number of times. This is not fair and should not be done unless the user has explicitly given consent.
Privacy is not an excuse
The scenarios described above are however not realistic as IP addresses on their own are not enough for that level of tracking. The point is that amazing experiences are not an excuse for an invasion of users’ privacy, while privacy is at the same time never an excuse for bad experiences.
The key is to earn trust, irrespective of whether you sell kettles or vacation destinations. If you can manage to win a user’s trust, commit to transparency and obtain consent, the user is likely to look forward to any holiday recommendations from you and will, without a doubt, accept deals for your kettles.
As ipapi.com combines granular control with raw power, this will allow you to achieve all of the above, simply and easily.
There are 45 data points in ipapi.com that can be returned in a lightweight XML or JSON format within milliseconds.
- Location: Country, Continent, City ZIP Code, Region, Longitude, Latitude, Capital, Geoname ID, Country Flag, Languages, EU Member Detection and Calling Code
- Time: Time Zone Code, Time Zone ID, GMT Offset, Daylight Saving Detection and Current Time
- Currency: Currency Name, Currency Code, Currency Symbol International, Currency Symbol Native and Currency Name Plural
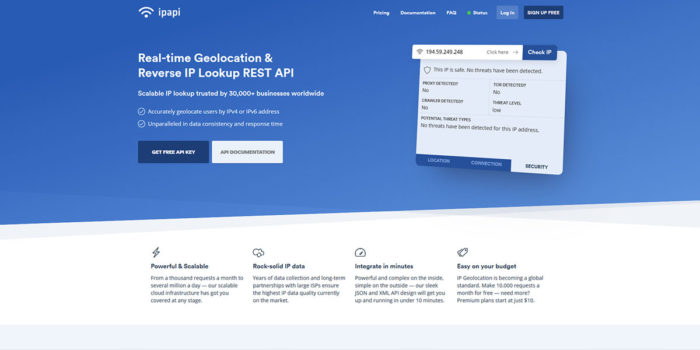
- Connection data: ISP, ASN, Crawler Detection, Proxy Detection, Threat Evaluation and TOR Detection
These data points can all be deployed via a sleek XML and JSON API design and it is typically possible to get started in less than 10 minutes. Although the API is very intuitive, detailed documentation is available should any help be needed.
Getting started
ipapi.com has a free plan that will assist new users in getting to know the system. The free level allows using location data to do up to 10,000 lookups per month. This limit can be increased to 50,000 searches per month with the use of location, connection data, time zone, or currency. The Standard plan sells for $10 per month and includes HTTPS encryption for lookups.
The Business package can be used for intensive scenarios at $50 per month offers up to 500,000 monthly lookups. Location, connection data, time zone, or currency can be used and HTTPS encryption is provided with bulk lookups.
The Pro package can be used for 2,000,000 monthly lookups at $100 per month. Location, connection data, time zone, security data, or currency can be used and HTTPS encryption is provided. A custom package is also available for high-volume requests.